STRANGE + WONDERFUL
RECENT STORIES
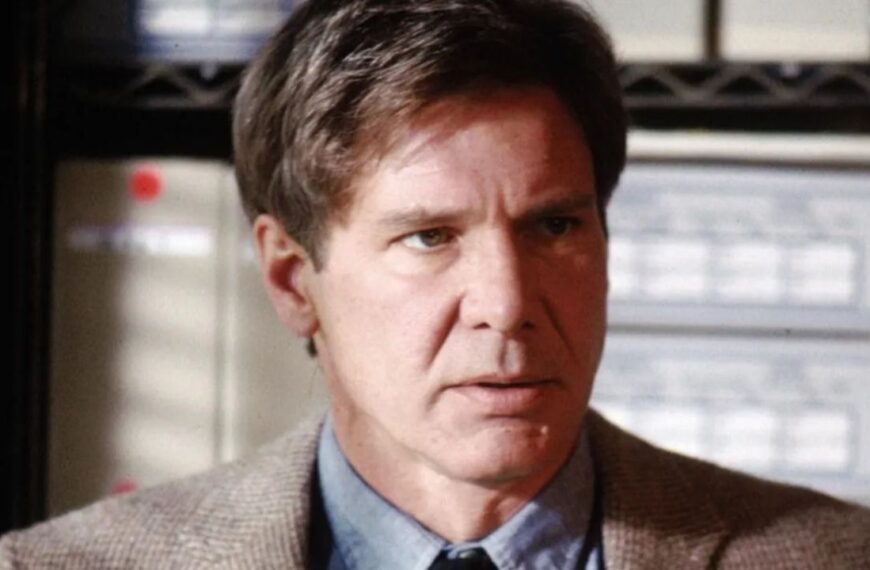
The Best Soundtracks in Video Games
Soundtracks can make or break the immersion level in a video game. Melancholy tunes add to the emotion during tragic moments, while creepy themes make horror titles even scarier. As with visual fidelity and gameplay scope, music quality also increases as newer technology becomes available. Over the years,…
Carrying A Tune: 15 Films That Celebrate Music
There is a difference between music fans and musical fans, just as there are differences between musicals and movies about music. The latter category…
12 Mistakes Daughters Secretly Wish Their Dads Would Stop Making
Being a dad is joyful torture in some ways. While you get the reward of watching your kids grow up, you also feel their…
15 Things Experienced Travelers Do – That You Should Too
Everybody loves going on an adventure, but not everyone knows the steps savvy travelers take to ensure their trip is as memorable as possible.…
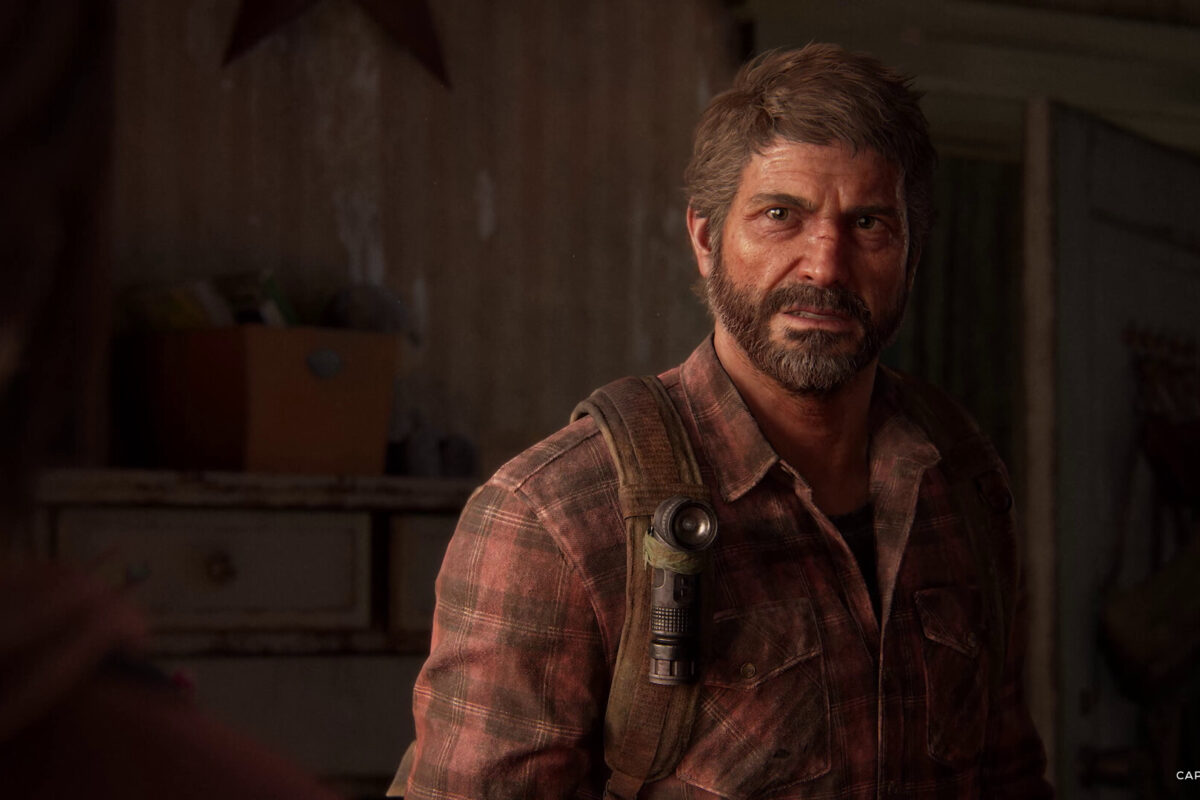
Popular British Bands That Somehow Didn’t Make It In America
The music industry is a fickle environment that’s becoming increasingly faceless. Average bands become world-famous, while authentic acts might struggle. British music once had…
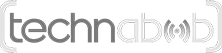
American Actors With the Best British Accents
I am a British subject living overseas — also known in Britain as a foreigner. Nonetheless, I still retain the exact English accent I…
15 Ways to Keep Your Brain Feeling 40, Even at Age 60 or Beyond
As our bodies age, our mental faculties age with them. Brain function changes as we age, and a decline can occur. Concerns over conditions…
12 Best Car Chases in Movie History
Few movie scenes are more entertaining than a classic car chase. Picture this: speeding cars weaving in and out of city traffic in a…