STRANGE + WONDERFUL
RECENT STORIES
15 Countries an American Can Move to and Save Money
America’s cost of living is high. Let’s just get that out of the way. This country ranks 12th for the highest cost of living in the world, according to Numbeo. Depending on your goals or current financial situation, you may be considering relocating abroad in exchange for more affordable…
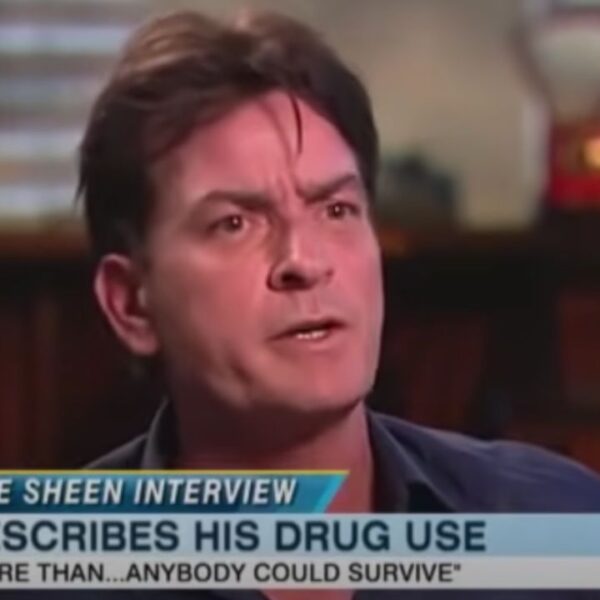
15 TV Interviews That Went Downhill Fast
Let’s be honest; most celebrity interviews are full of hot air, false platitudes, and boring small talk. The worst ones are when the celebrity…
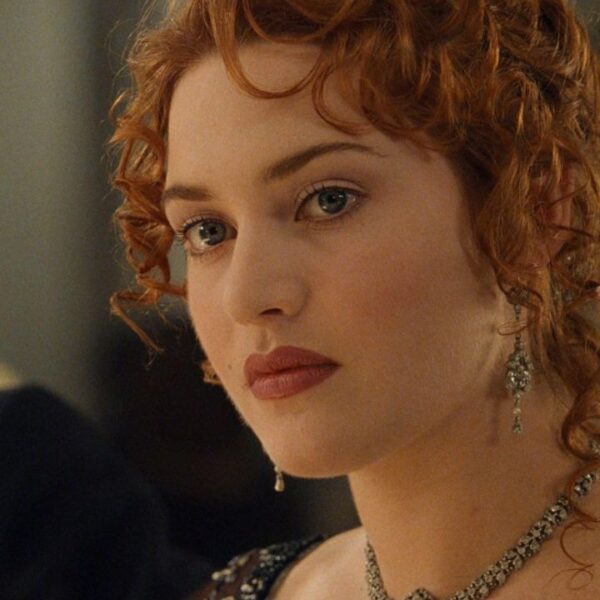
15 Biggest Cinematic Slip-Ups Caught on Camera
Making a movie involves many moving parts, and ensuring everything comes out perfectly is tough. However, it’s hard not to notice certain cinematic mistakes…
15 Personal Facts That Are Best Left Unshared
Contrary to popular belief, there is such a thing as offering “too much information.” Some things are better left unsaid, and this is a…
15 Nutritious Snack Options to Keep You Energized All Day
There’s nothing worse than the mid-day energy drain. You’re sitting at your desk. You’re hungry, losing focus, and counting down the minutes until you…
15 Sports That Keep People Healthy Without Going to the Gym
For those of you who want to avoid crowded gyms and rising fees, you might be looking for an activity to keep you fit.…
15 Guilty-Pleasure TV Shows We Love to Binge
From cheesy rom-coms that make you swoon to action-packed thrillers to spooky horror shows that make you shiver, there are endless TV shows to…
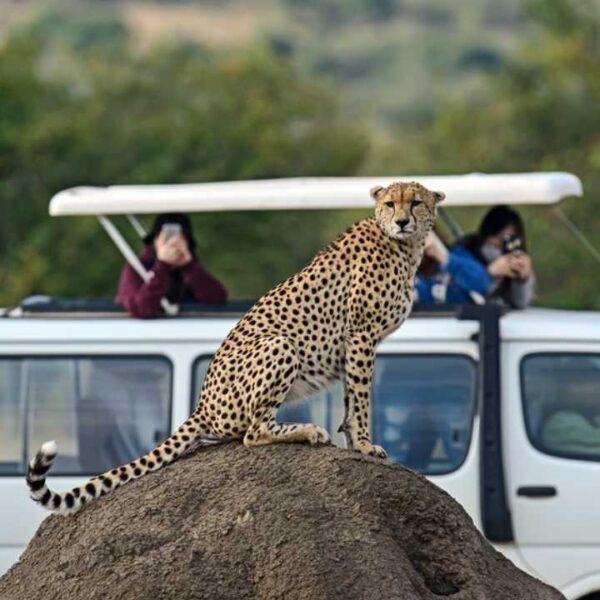
The 15 Best Countries for Wildlife Sightings
If you are an animal lover, you might find the opportunity to go on a safari or hike through a lush rainforest as a…