STRANGE + WONDERFUL
RECENT STORIES
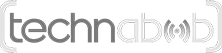
Great Movie Quotes That Instantly Give Away The Film
Great movies and great quotes go hand in hand. They become a part of its marketing campaign and can have a lasting impact, even long after a film’s release. The best lines from a movie are the ones we’re able to recite in our lives. Sometimes, movie fans…
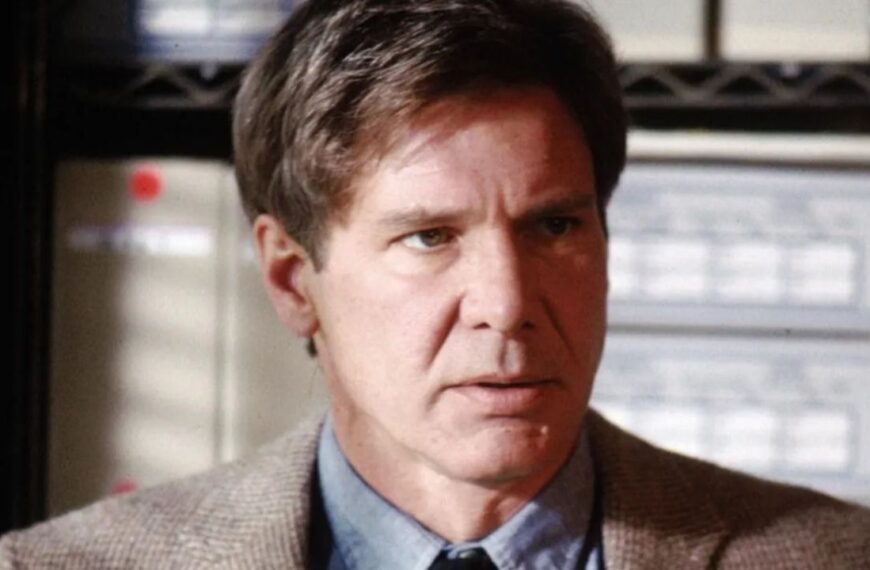
Beautiful Musical Performances That Will Make Anyone Emotional
Music has the power to transport us back to lost loves, first meetings, and happy moments. Some artists are able to enhance those emotions…
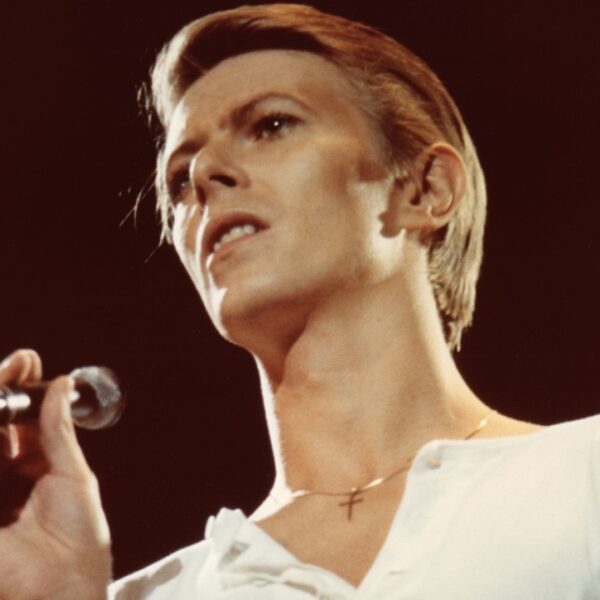
The 13 Voices We’d Love to Narrate Our Lives
Some voices are so soothing and intoxicating that we’d listen to them read the phone book. Some actors could make these obsolete things, such…
Once Acceptable Things That Are Now Very Inappropriate
As time changes, customs also change. Things that people once did routinely are now frowned upon. It’s not necessarily that they were misbehaving before;…
12 Iconic Movie Quotes That Are Incredibly Emotional
There’s nothing like a great movie quote. The best ones are able to be used in our everyday lives, usually for comic affect. But…
15 Things To Do Before Traveling Abroad – The Ultimate Checklist
You’ve booked your international flight, scored a unique Airbnb, and your anticipation is at a fever pitch. There’s nothing left to do than count…
Solo But Social: 15 Friendship Tips for Travelers in Their 40s
Adults often find it challenging to make new friends. This difficulty becomes even more pronounced during solo travel, especially for those dealing with social…
15 Surprising Things the Car You Drive Reveals About Your Personality
Ever wonder if your car reflects more than just your taste in vehicles? Sometimes, we read our astrology profile and think, wow, that sounds…